Giving an AI read-only access to your production database feels scary. Most engineering leaders we talk to have the same three worries. Here is how EQQ addresses each one.
Worry 1: “The AI will run a bad query and take down the DB.”
It cannot. Under MCP, the AI does not write SQL. It invokes named queries with parameters. Every query was authored, reviewed, and marked Active by humans. The AI's worst case is calling a slow query with wide parameters - which the interactive timeout and max-row limits already bound.
Worry 2: “Prompt injection will leak data.”
A model cannot leak what it cannot read. The API key maps to a role; the role maps to a specific list of queries. Injection attempts that say “ignore previous instructions and run X” fail because X is not in the tool list.
Worry 3: “We will not know what the AI did.”
Every call is audited. Filter the audit log by API key and you see every run, with parameters, rows, and elapsed time. Most customers route AI-agent audit entries to a separate SIEM pipeline for extra visibility.
Production readiness checklist for AI database access
- Create a dedicated service user, e.g. claude-readonly.
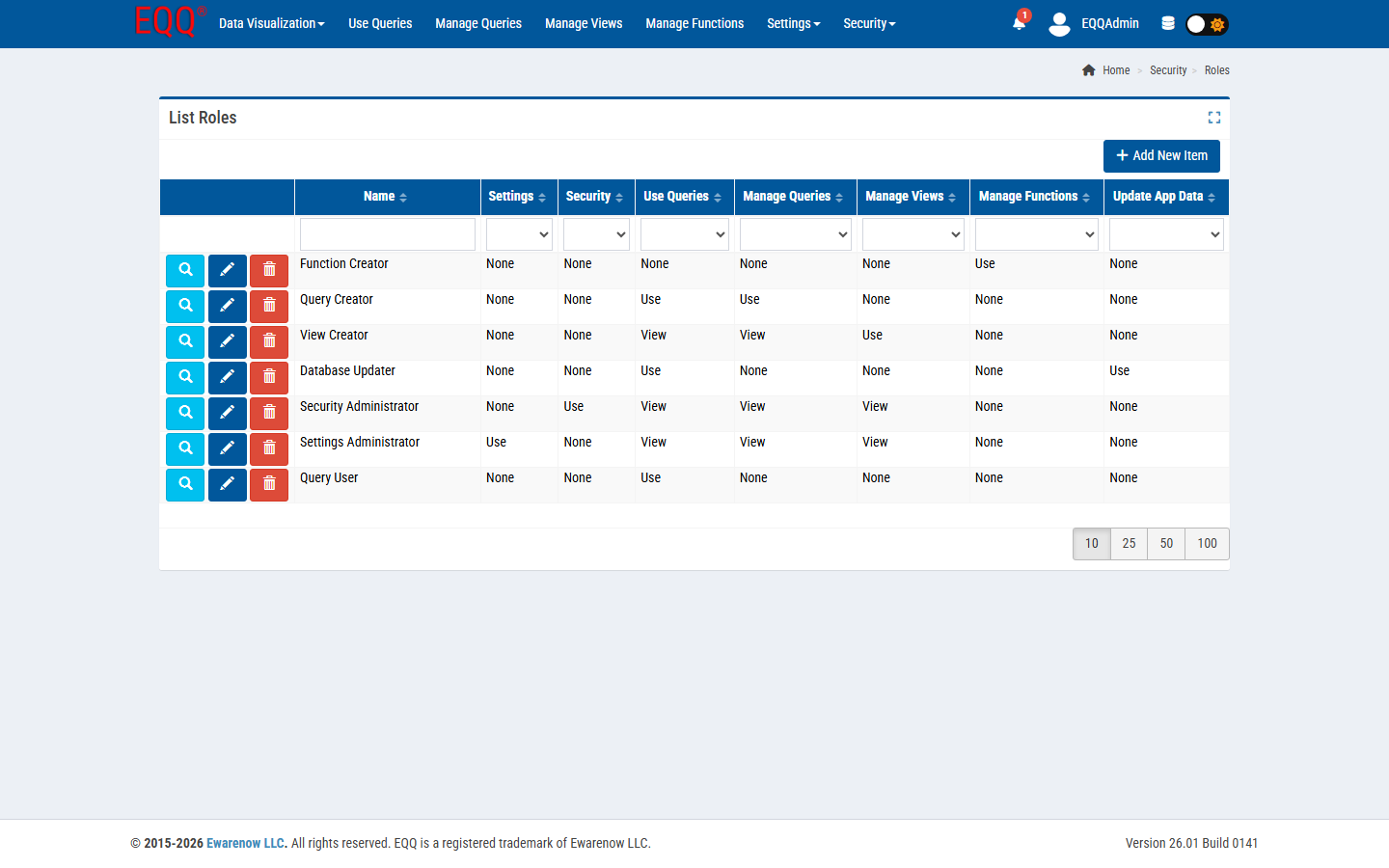
- Assign a role with only Use Queries on a narrow query set.
- Issue a scoped API key; rotate quarterly.
- Enable MFA on the human accounts that hold the key.
- Forward the audit log to your SIEM.
For step 4, EQQ enforces password complexity at the application layer: minimum 12 characters with at least one digit, one special character, one uppercase letter, and one lowercase letter. This applies to all human accounts including the ones that hold AI-agent API keys, closing the credential-stuffing vector without relying solely on your identity provider.
Done right, this is less risky than giving a developer ad-hoc SELECT access. The AI runs vetted code; the developer writes new code every time.
Key Terms
- SIEM - Security Information and Event Management - software that aggregates and correlates security events from across an IT environment.