“Sensitive data” is a broad word - salaries, PII, PHI, pricing, pre-release financials. The common thread is that most reads are fine and a few are catastrophic. EQQ gives you the knobs to separate the two without a custom app.
Three layers of scope that map to every major compliance framework
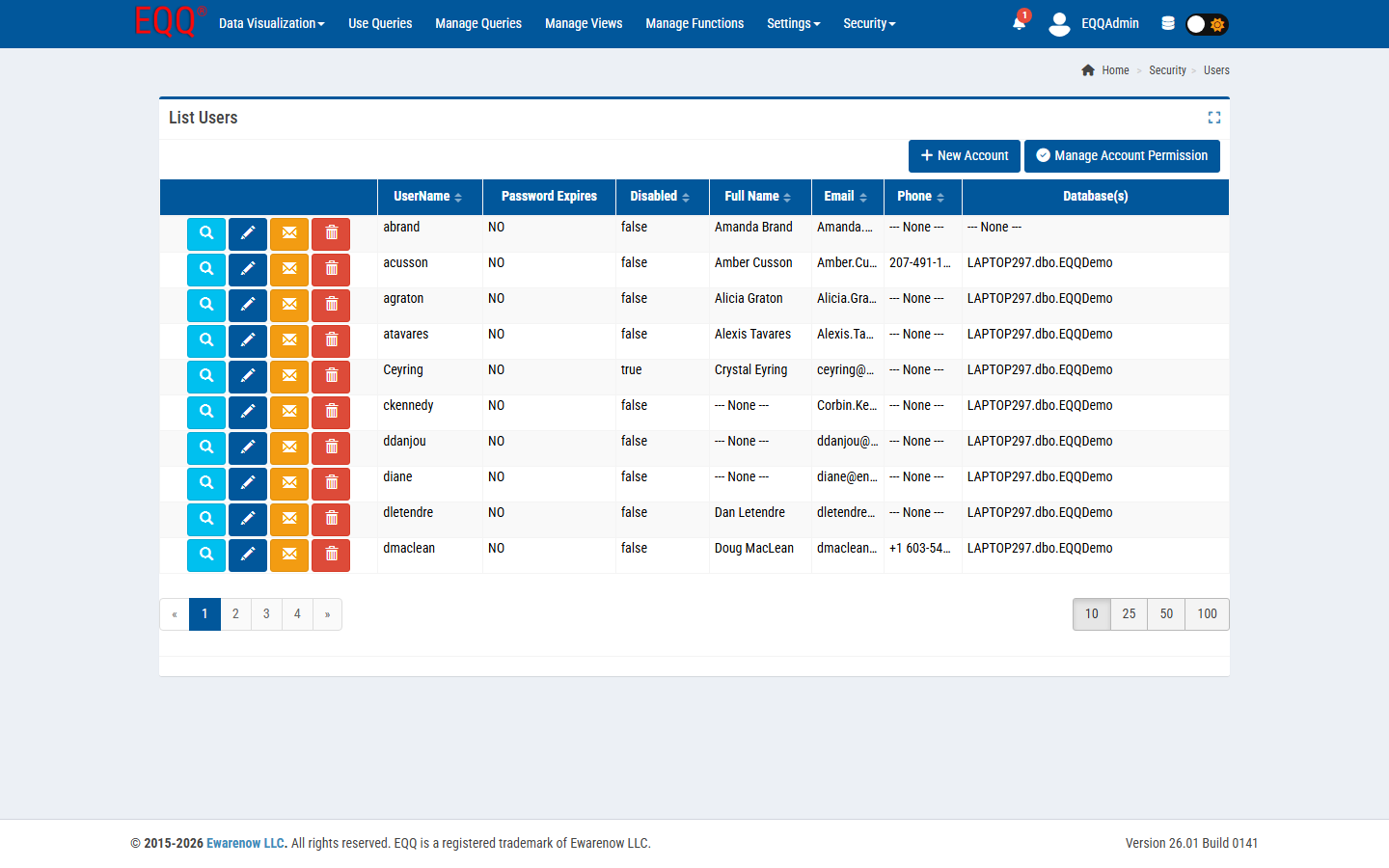
- Database scope. Each query belongs to a database connection; a user without access to that connection cannot see any of its queries.
- Role scope. Within a database, roles enumerate which queries a user can run.
- Row scope. Inside a query, a role-aware predicate (e.g.
Region = @UserRegion) filters the rows returned at execution time.
Each EQQ role is defined by seven permission columns that map directly to job functions. The full set is: Settings, Security, Use Queries, Manage Queries, Manage Views, Manage Functions, and Update App Data. A read-only analyst role typically gets only Use Queries; a query author gets Manage Queries in addition; only system administrators hold Settings and Security. This granularity means you can grant an AI API key exactly Use Queries on a named subset without any risk of it modifying definitions or security configuration.
Mask sensitive columns so raw values never leave the database
For columns like SSN or email, use a Function (fQQ_MaskEmail) in the View so the raw column never leaves the database. The user sees a***@example.com; the raw value is only visible to roles that join directly against the View that does not apply the mask.
API key scoping keeps integrations isolated and revocable
Every API key inherits exactly the permissions of the user that owns it. Issue a separate key per integration; revoke independently; rotate without coordinating with other integrations.
Compliance mapping: how EQQ controls satisfy SOX, HIPAA, and GDPR
- SOX - state-machine lifecycle + audit trail = change control.
- HIPAA - row-level predicates + masking = minimum necessary.
- GDPR - audit trail + named integrations = records of processing.
Key Terms
- PII - Personally Identifiable Information - any data that can identify a specific individual, such as name, email address, or national ID number.
- PHI - Protected Health Information - health-related data covered by HIPAA that links to an identifiable patient.
- SSN - Social Security Number - the US government-issued nine-digit identifier assigned to individuals for tax and benefits purposes.
- GDPR - General Data Protection Regulation - EU law that governs how personal data of EU residents may be collected, stored, and processed.
- HIPAA - Health Insurance Portability and Accountability Act - US law mandating the protection of patient health data.
- SOX - Sarbanes-Oxley Act - US law requiring auditable controls over financial data and reporting.